90%
of manual processes automated
6 Million+
business-critical transactions a day
$120 Billion
of revenue among customers
It’s just so robust and it’s really geared to that vertical market. As a result, everything you need is right there: the compliance pieces, the overtime…those things that make a business better and operate more efficiently are built in.”
– Allied Universal
The biggest benefit is having all the data in one spot and getting up-to-the-second job costing. When we look at financials at a high level, it’s hard to see where the problems are. With job costing, you can actually see trends at each job.”
– Janitronics
Why
TEAM Software
Proven Industry Focus and Expertise
With more than 30 years of serving cleaning and security contractors with distributed workforces, our industry longevity is unmatched.
Exceptional Customer Experience
Our collaboration, responsiveness and commitment to value-driven innovation have led to a year-over-year customer retention rate of better than 90%.
Powerful, Scalable Solutions
Designed to scale, our solutions support nearly 1 million end users – from growing mid-sized companies to large global operators with complex needs.
Growth-Enabling Profitability
Our software drives efficiency and productivity, while reducing risk and costs. That kind of profitability sets the stage for significant growth.
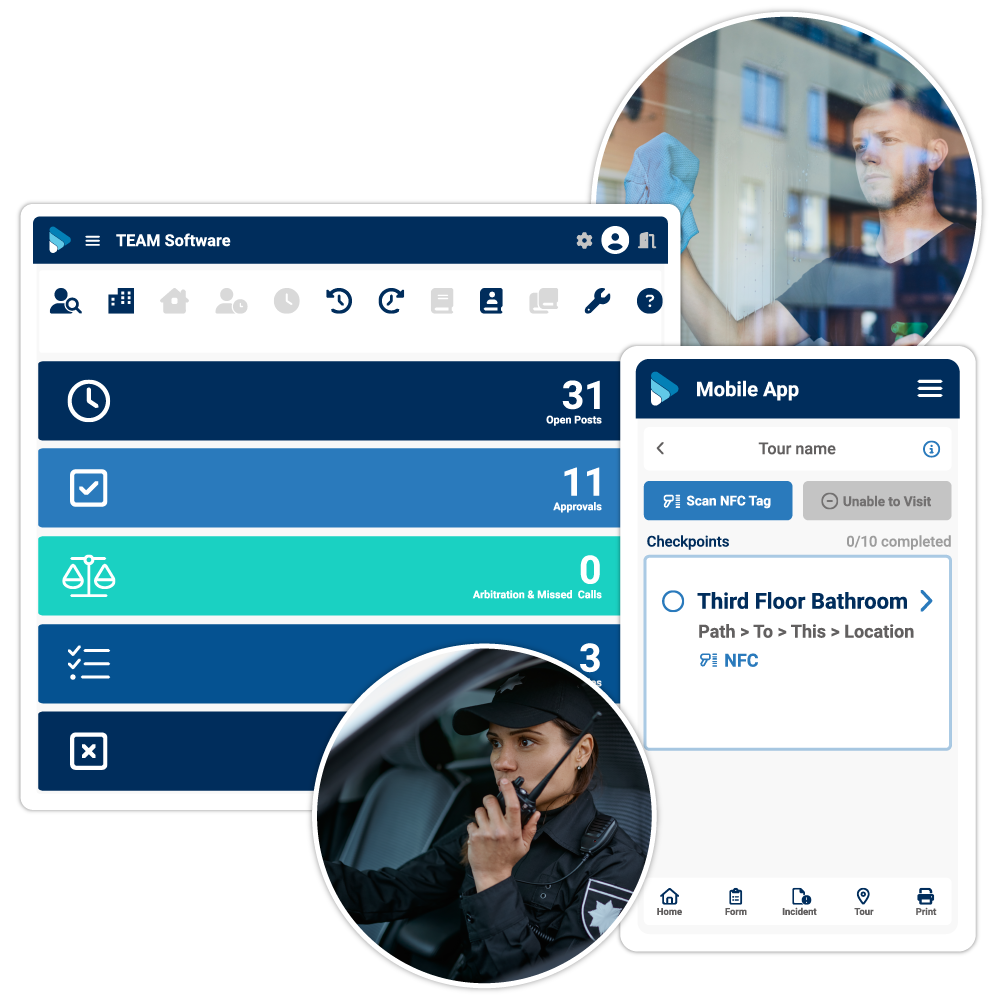
Business Solutions
Discover our unrivaled portfolio of industry-specific software solutions. See how our technology can simplify operations and grow your business over time.
Connect with Your Workforce
Engage your workforce with tools to direct, set and track field-based operations.
Deliver on Promises
Discover our solutions designed to help you deliver on and exceed customer expectations.
Run A Smarter Operation
Increase efficiency and productivity with operations tools that help your teams perform and make decisions effectively.
Additional Resources
One quick form before you can read this.
Complete this form to access helpful information to help you grow your business.